Despite GitHub’s efforts to prevent repository hijacking, cybersecurity researchers continue finding new attack methods, and thousands of code packages and millions of users could be at risk.
Repojacking is a repository hijacking method that involves renamed GitHub usernames. If a user renames their account, their old username can be registered by someone else, including malicious actors, and potentially abused for supply chain attacks.
Threat actors may be able to register an old username and create repositories that were previously associated with the old username, which could allow them to route traffic intended for the legitimate repository to their malicious repository.
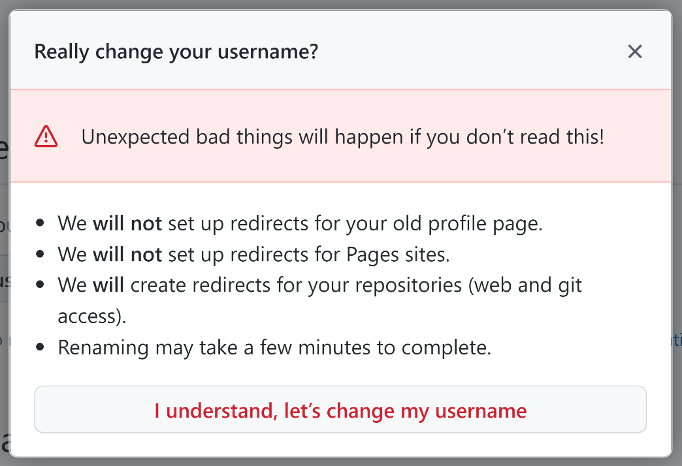
In order to prevent such attacks, GitHub has been implementing a retired namespace protection mechanism and it has been warning users about the potential risks associated with changing usernames.
The namespace is the combination between the username and a specific repository name — for example, github.com/username/repo_name. If a user changes the username, the old username’s new owner cannot create a repository named ‘repo_name’ if the repository was previously cloned 100 times. This means that GitHub has retired the namespace.
The problem is that researchers continue finding ways to bypass GitHub’s namespace retirement mechanism and conduct repojacking.
The most recently disclosed attack method was discovered by researchers at cybersecurity firm Checkmarx in March and it was recently fixed by GitHub.
This new method leveraged a race condition, with an API request being used to almost simultaneously create a new repository and change the account’s username.
If the attacker renames their account to the targeted username and later attempts to create a repository that would result in the creation of a retired namespace, their attempt would be blocked.
However — before GitHub rolled out a fix — if the account renaming and the repository creation were done at the same time, the attempt would be successful, enabling the attacker to obtain a namespace that would allow them to redirect traffic to their malicious repository.
Checkmarx’s analysis showed that roughly 4,000 code packages in Go, PHP, Swift, as well as GitHub Actions were impacted, including hundreds of packages with more than 1,000 stars.
“Poisoning a popular GitHub action could lead to major Supply Chain attacks with significant repercussions,” Checkmarx warned.
The problem is that these packages will continue to be vulnerable to repojacking if a new bypass method is discovered in the future.
“The discovery of this novel vulnerability in GitHub’s repository creation and username renaming operations underlines the persistent risks associated with the ‘Popular repository namespace retirement’ mechanism,” Checkmarx said in a blog post.
It added, “Many GitHub users, including users that control popular repositories and packages, choose to use the ‘User rename’ feature GitHub offers. For that reason, the attempt to bypass the ‘Popular repository namespace retirement’ remains an attractive attack point for supply chain attackers with the potential to cause substantial damages.”
The security firm has released an open source tool named ChainJacking that can be used to identify vulnerable packages.
Related: Developers Warned of Malicious PyPI, NPM, Ruby Packages Targeting Macs
Related: ChatGPT Hallucinations Can Be Exploited to Distribute Malicious Code Packages
Related: Malicious NuGet Packages Used to Target .NET Developers


